Most people think a password is strong because it “looks complicated.” But security researchers measure password strength using a precise concept called password entropy — and it tells a very different story than what most people expect.
In this guide you will learn exactly what password entropy is, how long it would take to crack your password with modern hardware, whether your password has appeared in a data breach, and the difference between a passphrase vs password. By the end, you will know exactly how strong your password really is.
Want an instant answer? Our free tool checks your password entropy score, estimates crack time, and detects breaches — all offline, nothing is ever stored or sent to a server.
🔐 Check My Password Entropy Free →What Is Password Entropy? (Simply Explained)
Password entropy is a mathematical measurement of how unpredictable your password is. It is expressed in bits. The higher the number, the harder your password is to crack.
Think of it this way: a coin flip has 1 bit of entropy — two equally likely outcomes. Every bit you add to a password doubles the number of guesses an attacker needs. A password with 40 bits of entropy requires over 1 trillion guesses. A password with 60 bits requires over 1 quintillion.
This is why length matters far more than complexity. Adding one more character to your password adds more entropy than adding a symbol to a short password.
| Entropy (bits) | Strength Level | Example | Crack Time (modern GPU) |
|---|---|---|---|
| Below 28 bits | 🔴 Very Weak | dog123 | Instant |
| 28 – 35 bits | 🔴 Weak | MyDog2019 | Minutes to hours |
| 36 – 59 bits | 🟡 Fair | M#d0g!2024x | Days to months |
| 60 – 79 bits | 🟢 Strong | Xk@9mP!qL2#nRt | Decades to centuries |
| 80+ bits | 🟢 Very Strong | 16+ char random | Longer than human history |
How Long Would It Take to Crack Your Password?
The crack time of a password depends on two things: its entropy, and the speed of the attack. Modern consumer GPUs can test billions of password combinations per second. Here is what that means for real passwords:
| Password | Length | Character Types | Crack Time |
|---|---|---|---|
| simple | 6 chars | Lowercase only | < 1 second |
| MyDog123 | 8 chars | Mixed + number | ~3 hours |
| P@ssw0rd! | 9 chars | All types | ~2 days |
| Xk@9mP!qL2 | 10 chars | All types | ~6 months |
| Xk@9mP!qL2#n | 12 chars | All types | ~200 years |
| correct-horse-staple-2026 | 25 chars | Passphrase + number | Centuries |
Notice that P@ssw0rd! — which most people think looks very secure — cracks in just 2 days. This is because attackers specifically program their tools to try common substitution patterns like replacing “a” with “@” or “o” with “0”. A truly random 12-character password is dramatically safer.
Passphrase vs Password — Which Is Stronger?
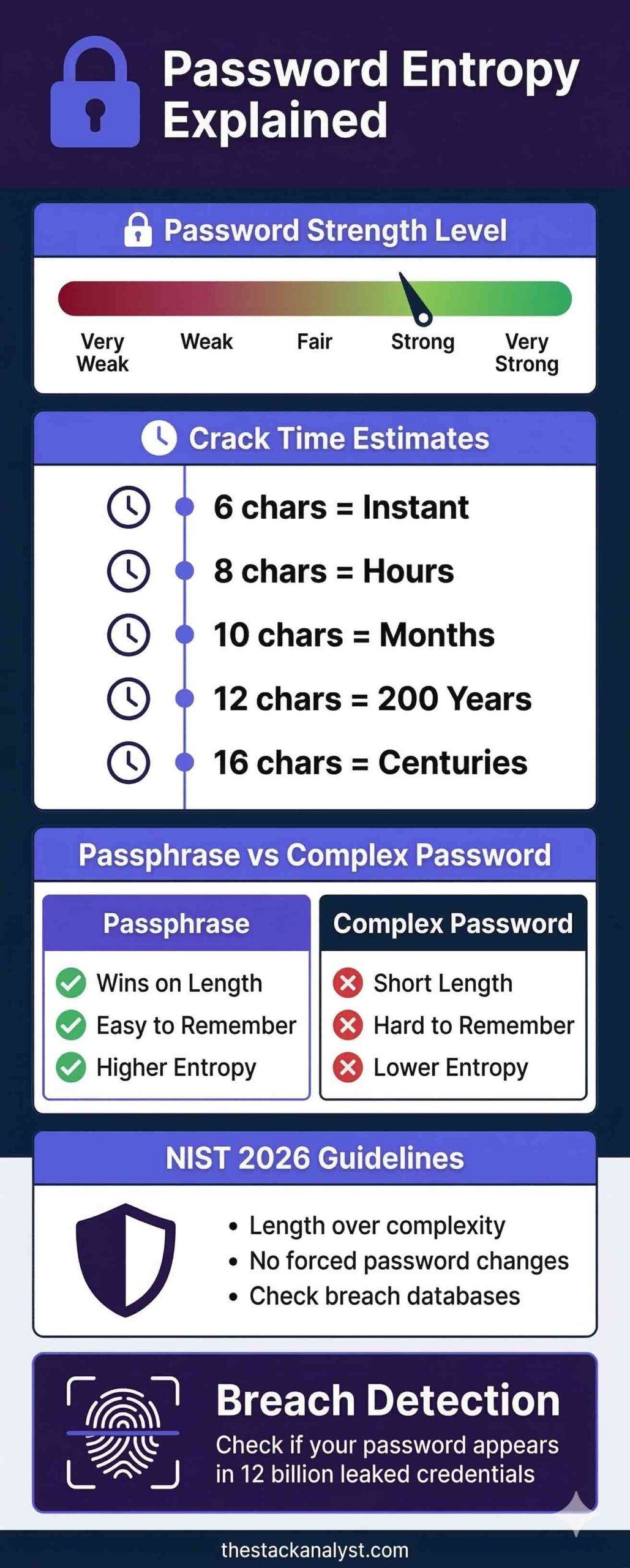
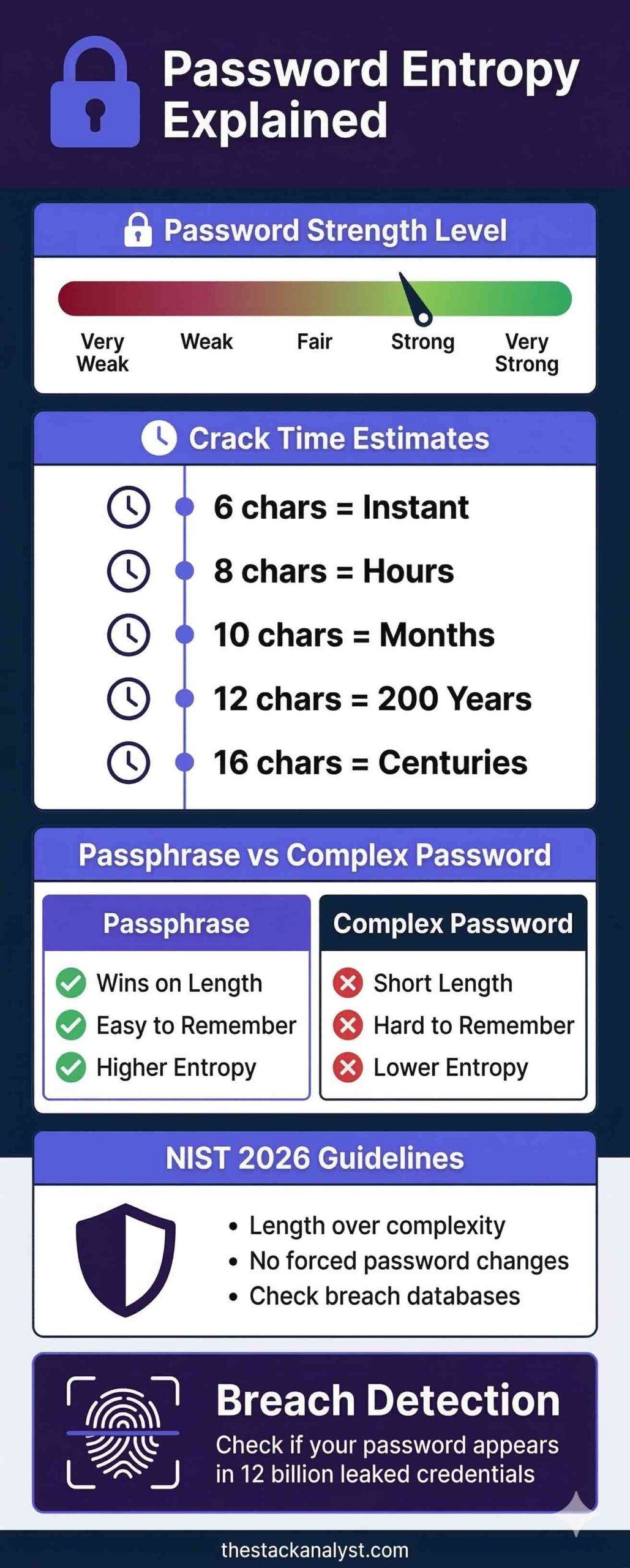
This is one of the most misunderstood topics in everyday security. Most people believe a short, complex password like X#9mP!2k is stronger than a long phrase like correct-horse-staple-battery. They are wrong.
Why a Passphrase Wins on Entropy
The phrase correct-horse-staple-battery is 30 characters long. Even though it only uses lowercase letters and hyphens, its length gives it an entropy of over 100 bits — far beyond what any current hardware can crack in any reasonable timeframe.
| Short Complex Password | Passphrase | |
|---|---|---|
| Example | X#9mP!2k | correct-horse-staple-battery |
| Length | 8 characters | 28 characters |
| Entropy | ~52 bits | ~100+ bits |
| Crack time | Weeks to months | Centuries |
| Easy to remember? | ❌ No | ✅ Yes |
For most people, a passphrase of 4–5 random, unrelated words is the best balance of security and memorability. Add a number or symbol somewhere in the middle for extra entropy.
Is My Password in a Data Breach?
Even a perfectly strong password becomes worthless if it has already been stolen in a data breach and is circulating in hacker databases. This is called a credential stuffing attack — attackers take leaked username and password combinations and try them on hundreds of sites automatically.
The Have I Been Pwned database contains over 12 billion breached passwords from thousands of real data breaches. Our password strength checker checks your password against this database using a method called k-anonymity — only the first 5 characters of a scrambled hash are ever transmitted, not your actual password. It is completely private.
- Your password is never sent to any server in plain text
- The check works even if you disconnect your internet mid-test
- No account or registration is required
- Results are instant and shown only in your browser
NIST Password Guidelines 2026 — What the Experts Say
The US National Institute of Standards and Technology (NIST) publishes SP 800-63B — the most widely followed password security guidelines in the world. Their latest recommendations have changed significantly from older advice:
- Prioritise length over complexity — a 20-character lowercase password beats an 8-character one with symbols
- Do not force regular password changes — change only when there is evidence of compromise
- Check against breach databases — block passwords known to be compromised
- Allow all printable characters including spaces — passphrases with spaces should be permitted
- No complexity rules — do not force users to include uppercase, numbers, or symbols
- Minimum 8 characters for user-set passwords, 6 for system-generated ones
The core shift in NIST guidelines is clear: length is the most important factor. A long, memorable passphrase is now officially recommended over a short, complex password that users write down or forget.
Common Password Mistakes That Reduce Entropy
- Using the same password across multiple sites (breach on one = breach on all)
- Adding “1!” at the end of a dictionary word — attackers try this first
- Replacing letters with similar numbers (a→4, e→3, o→0) — tools are programmed for this
- Using your name, pet name, birthday, or city
- Using a password under 12 characters, no matter how complex it looks
- Saving passwords in a notes app, spreadsheet, or plain text file
How to Check Your Password Entropy Right Now
Our free password strength checker gives you an instant entropy score in bits, estimated crack time, breach detection, and specific improvement suggestions — all processed locally in your browser. Zero data leaves your device.
🔐 Check My Password Entropy →Frequently Asked Questions
What is password entropy and why does it matter?
Password entropy is a mathematical measure of how unpredictable your password is, expressed in bits. The higher the entropy, the more guesses an attacker needs to crack it. Aim for at least 60 bits of entropy for everyday accounts and 80+ bits for email or banking passwords. Our free password strength checker shows your exact entropy score in bits.
How long does it take to crack a password?
It depends entirely on the password length and entropy. A 6-character lowercase password cracks in under a second with modern hardware. A 12-character random password using all character types would take roughly 200 years. A 16+ character passphrase would take centuries. The best way to know is to use a crack time estimator — our password checker tool shows this for every password you test.
Is a passphrase stronger than a complex password?
Yes, in almost every case. A passphrase like “correct-horse-staple-battery” (28 characters) has significantly higher entropy than a short complex password like “X#9mP!2k” (8 characters), even though the passphrase only uses lowercase letters. Length contributes more to entropy than character variety, which is why NIST now recommends passphrases over short complex passwords.
How do I know if my password is in a data breach?
You can check using our password checker tool, which checks against the Have I Been Pwned database of over 12 billion breached passwords. It uses k-anonymity — only a partial hash is transmitted, never your actual password. If your password appears in a breach, change it immediately on every site where you use it.
What are the NIST password guidelines for 2026?
NIST SP 800-63B recommends prioritising password length over complexity, not forcing regular password changes unless there is evidence of compromise, checking passwords against known breach databases, and allowing all printable characters including spaces. The minimum recommended length is 8 characters, but 15+ is strongly preferred for real security.
Is it safe to type my password into an online checker?
Only if the tool processes your password locally in the browser. Many online checkers send your password to their server, which is a serious security risk. Our password strength checker runs entirely in your browser — nothing is ever transmitted to a server. You can verify this by disconnecting from the internet and testing it; it still works perfectly.
What is the strongest type of password I can create?
A randomly generated 16+ character password using uppercase, lowercase, numbers, and symbols stored in a reputable password manager is technically the strongest. As a memorable alternative, a passphrase of 5+ random unrelated words gives you very high entropy while remaining easy to remember. Avoid using any real words, names, or phrases you would naturally think of.






